Introduction
A fintech receives notice of a regulatory exam from their bank partner or FinCEN examiner. Within hours, the team is scrambling — hunting for the latest board-approved policies, pulling together transaction monitoring disposition records, and reconstructing SAR filing timelines from emails and spreadsheets. The stress is palpable, and the gaps are immediately obvious.
This reactive scramble is the most common — and most preventable — compliance failure in the fintech and payments space. It signals a program that exists on paper but hasn't kept pace with the business it's meant to protect.
Fintechs and payments companies are built to move fast, but regulatory expectations around financial crime compliance don't slow down to match growth. A program that can't demonstrate effectiveness under scrutiny is a liability — regardless of how well the underlying controls actually work.
When examiners arrive, they evaluate evidence, not intent.
TLDR:
- Audit readiness means your FinCrime program can withstand examiner scrutiny at any point, not just during exam season
- Strong programs rest on five documented pillars: internal controls, a compliance officer, independent testing, training, and customer due diligence
- Continuous compliance eliminates the reactive scramble before an examiner ever arrives
- Common exam failures stem from stale risk assessments, undocumented transaction monitoring changes, and weak SAR narratives
- Expert advisory support closes the gap between where a program is and where it needs to be before an examiner arrives
Why FinCrime Regulatory Exams Are Raising the Stakes
Fintechs and payments companies face layered oversight: federal regulators like FinCEN and the OCC, state regulators, and increasingly rigorous bank sponsor oversight programs—all of which evaluate BSA/AML program quality and may conduct formal exams or compliance reviews.
Enforcement actions have grown sharper. Binance paid $4.3 billion in 2023 for willful failure to register as an MSB and implement an effective AML program. Block/Cash App paid $80 million to state regulators for BSA/AML violations, including a backlog of 169,000 unresolved transaction monitoring alerts.

The De-Risking Threat
Beyond regulatory fines, fintechs face an existential threat: bank partners routinely audit their fintech clients' compliance programs before granting or renewing sponsorship access. A failed review can mean loss of the banking relationship. In 2024, Blue Ridge Bank completely exited its Banking-as-a-Service program after peaking at 70+ partnerships, with the CEO noting that "the volume outran the capacity of the bank to run it the right way." This isn't a compliance pressure that ends in a fine—it ends in business shutdown.
Expanding Examiner Expectations
Regulators now expect documented evidence of program effectiveness, not just the existence of policies. The April 2020 FFIEC BSA/AML Examination Manual updates explicitly shifted examiner focus toward "Risk-Focused BSA/AML Supervision," instructing examiners to evaluate program effectiveness based on actual outcomes rather than policy binders with board signatures. Examiners now specifically assess:
- SAR filing timeliness
- Alert disposition quality
- KYC completeness
What Audit Readiness Really Means for Financial Crime Compliance
Audit readiness in the FinCrime context means demonstrating that a functioning, risk-calibrated program exists and is operating as designed—with documented decisions, traceable workflows, and measurable outcomes. A policy binder alone won't satisfy an examiner. The evidence has to show the program actually runs the way the documents say it does.
Paper vs. Practice
A compliance program that exists "on paper" may have all the right documents: board-approved policies, a designated BSA officer, training completion logs. But examiners evaluate outcomes. They look at:
- SAR filing timeliness and narrative quality
- Alert disposition rates and documented rationale
- KYC/EDD completeness for high-risk customers
- Evidence that the risk assessment reflects current operations
A program that can't produce this evidence fails the exam, even if the policies are perfect.
What Regulators Evaluate
During a FinCrime exam, regulators specifically evaluate:
- Currency of the enterprise-wide risk assessment — does it reflect current products, customer segments, and geographies?
- Transaction monitoring model rationale and tuning documentation — are threshold changes documented and justified?
- SAR filing quality — are narratives complete, timely (within 30 days), and supported by escalation trails?
- CDD/EDD records — are customer risk profiles current and documented?
- Training completion logs — is training role-specific and tested for comprehension?
Continuous-State Evaluation
Many fintechs are examined by both regulators and bank partners on staggered cycles. This means audit readiness must be a permanent posture, not a surge activity before a known deadline. That posture has a practical definition: documentation current, workflows traceable, and evidence producible on any given day—not assembled under deadline pressure.
The Five-Pillar Framework
That permanent posture has a structural foundation. Federal examiners use the "5 Pillars" framework for BSA/AML compliance as their evaluation baseline:
- Internal controls to assure ongoing compliance
- Designation of a qualified BSA/AML compliance officer responsible for coordinating day-to-day compliance
- Ongoing training for appropriate personnel
- Independent testing to monitor program adequacy
- Customer identification and due diligence program with risk-based procedures
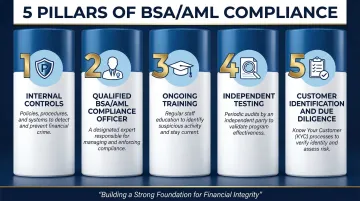
A strong program maps all documented evidence to each of these pillars. Missing documentation in any pillar is a red flag.
The Building Blocks of an Audit-Ready FinCrime Program
Written Policies and Procedures
Policies must be current, board-approved, role-specific, and tied to the actual products, customer segments, and channels the organization operates. Generic or boilerplate policies are a significant examiner red flag. Policies should be reviewed and updated when the business model changes, not on a fixed calendar alone.
Enterprise-Wide Risk Assessment
This is the cornerstone document regulators evaluate first. It must:
- Reflect current products, geographies, delivery channels, and customer types
- Include a documented methodology
- Be updated whenever material changes occur (new products, customer segments, acquisitions)
A stale risk assessment signals a program that is not keeping pace with business growth. Regulators consistently cite outdated risk assessments in enforcement actions.
Transaction Monitoring Documentation
Running a transaction monitoring system is not enough. Organizations must:
- Document alert disposition decisions in real time
- Record model tuning rationale and threshold changes with senior management approval
- Track false positive rates over time
- Demonstrate that the system is calibrated to the risk profile in the risk assessment
Undocumented transaction monitoring changes are among the most common exam findings.
SAR Filing Quality and Escalation Trails
Examiners evaluate not just whether SARs were filed, but whether:
- Narratives are complete (who, what, when, where, why, how)
- Filings are timely (within the 30-day regulatory window)
- Each SAR is supported by a documented escalation path from initial alert through investigation to filing decision
Training and Awareness Records
Training must be:
- Role-specific, not one-size-fits-all
- Documented with completion records and comprehension testing
- Delivered at onboarding, annually, and for high-risk roles like customer onboarding and operations
Generic training completion logs without role-specificity are a red flag.
Each of these pillars depends on documentation that reflects how the organization actually operates — not how it was designed to operate two years ago. Pillars FinCrime Advisory works with fintechs and payments companies across all five areas, from drafting risk assessments that match current business models to optimizing transaction monitoring thresholds and preparing SAR escalation trails that hold up under examiner scrutiny.
Shifting from Reactive to Continuous Compliance
The Audit Fatigue Cycle
Fast-scaling fintechs commonly develop an audit fatigue cycle: the business grows rapidly, compliance infrastructure lags behind, and the team finds itself in crisis mode every time an exam or bank partner review approaches. This cycle is not just stressful—it's operationally dangerous because it means controls are only validated reactively, after gaps have already accumulated.
What Continuous Compliance Looks Like
In practice, continuous compliance for a FinCrime program means:
- Reviewing policies on a documented schedule
- Updating the risk assessment when products or customer segments change
- Documenting alert disposition decisions in real time
- Tracking SAR filing deadlines proactively
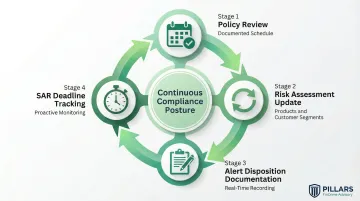
When compliance is continuous, examiners aren't finding gaps—they're confirming controls that were already working.
Regular Self-Assessments and Mock Exams
Quarterly internal reviews are one of the most effective ways to stay ahead of examiners. Map each review to the FFIEC BSA/AML Examination Manual's evaluation criteria, then:
- Simulate examiner document requests to surface gaps early
- Remediate findings before the actual exam — not during it
- Document the review process itself as evidence of program diligence
Independent Testing as a Diagnostic Tool
BSA regulations require periodic independent testing of the AML program — but the requirement is the floor, not the ceiling. Programs that treat independent reviews as a forward-looking diagnostic get far more value from the process. A reviewer brought in before an exam can surface blind spots that internal teams, too close to the program, routinely miss.
Red Flags Examiners Find in Fintech and Payments Programs
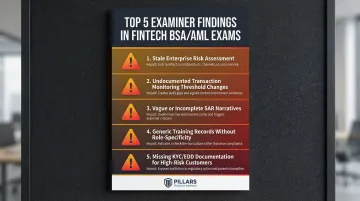
Most Common Findings
Examiners frequently cite these deficiencies in fintech and payments company exams:
- Stale enterprise-wide risk assessments that don't reflect current products or customer segments
- Transaction monitoring threshold changes with no documented rationale or senior management approval
- SAR filings with vague, incomplete, or templated narratives lacking the five essential elements (who, what, when, where, why)
- Training records showing generic completion but no role-specificity or comprehension testing
- Missing or inconsistent KYC/EDD documentation for high-risk customers
These findings often occur together because they stem from the same root cause: a program that grew alongside the business on paper but not in practice.
Why Growth Creates Vulnerability
Each new product launch, customer segment, partnership, or acquisition creates a compliance gap if the risk assessment and controls aren't updated in parallel. That lag between business growth and compliance infrastructure is the most direct path to examiner findings.
The Value of Pre-Exam Reviews
A pre-exam audit readiness review maps your current program against examiner expectations, surfaces documentation gaps, and produces a prioritized remediation plan before scrutiny begins. Pillars FinCrime Advisory's audit readiness and program assessment services give compliance teams a clear picture of where they stand — and what to fix — before an examiner arrives.
Frequently Asked Questions
How do compliance management solutions help organizations stay audit-ready?
Compliance management solutions centralize documentation, automate monitoring, and maintain continuous evidence trails. Examiners expect real-time, demonstrable evidence of program effectiveness—not after-the-fact reconstruction from emails and spreadsheets.
What is audit readiness and how can organizations improve it?
Audit readiness is the ability to demonstrate a functioning, effective compliance program at any point in time. Organizations improve it by shifting from reactive, exam-season preparation to continuous program management including regular self-assessments, updated documentation, and independent testing.
What is an IT compliance audit?
An IT compliance audit evaluates whether an organization's technology systems, controls, and data practices meet regulatory or internal standards. For fintechs and payments companies, this intersects with FinCrime compliance when transaction monitoring systems, data integrity, and access controls are part of the regulatory examination scope.
What are the 3 C's of compliance?
The 3 C's are Culture, Controls, and Communication (some versions use: Comply, Correct, and Confirm). Culture sets the tone that drives compliance behavior; Controls enforce it through processes and systems; Communication maintains transparency and accountability. In financial crime compliance, culture carries extra weight—regulators treat it as a leading indicator of overall program health.
What do regulators look for in a fintech BSA/AML compliance exam?
Regulators evaluate the enterprise-wide risk assessment, internal controls, transaction monitoring documentation, SAR filing quality, CDD/KYC program strength, training records, and the independence of the testing function. The exam covers both the existence and the demonstrated effectiveness of each program element.
How often should fintechs and payments companies update their AML risk assessment?
The risk assessment should be reviewed at least annually and updated whenever a material change occurs—such as a new product launch, new customer segment, new delivery channel, or significant growth in transaction volume. Regulators view a static risk assessment as a significant indicator of a program not keeping pace with business risk.