Introduction: Beyond the Binder
An exam notification lands in your inbox. The scramble begins — digging through shared drives, searching old emails, and flipping through policy binders to reconstruct a compliance posture that should have been documented all along. For many FinCrime compliance teams at fintechs, payments companies, and financial institutions, this plays out more often than it should.
That scramble exposes a critical gap: a binder full of policies is documentation, not a compliance program. Regulators and independent auditors don't just want to see your policies — they want proof that your controls operated consistently, that your team was trained, and that your transaction monitoring decisions were documented and defensible.
FinCEN, the OCC, FDIC, and state regulators assess compliance based on what you did, not what you intended to do.
This article explains what audit-ready actually means in the FinCrime context, how to architect a system that holds up under exam pressure, and what evidence regulators will specifically look for across the five pillars of a BSA/AML program.
TLDR: What You'll Learn
- Audit-ready compliance means maintaining living evidence that your FinCrime controls operated as designed — not just having a binder.
- The biggest audit risk is fragmentation: siloed policies, training records, and TM alert dispositions with no connective thread.
- Audit readiness requires traceability across five areas: policies, internal controls, a compliance officer, training, and independent testing.
- Proactive readiness through mock exams and gap analyses separates confident exam outcomes from last-minute scrambles.
Why the Binder Breaks: Static Compliance Docs and FinCrime Audit Risk
Static policy documents and periodic cleanup create the illusion of compliance — but they don't provide the operational evidence regulators actually require. During a FinCrime exam, a policy binder tells the examiner what your program is supposed to do. What they're looking for is proof that it did it.
That distinction is where most audit failures begin.
What examiners want vs. what the binder provides:
- Decision trails: Who reviewed the alert, what they concluded, and when — not just that alerts were reviewed
- Risk-based rationale: Documentation showing why a customer was tiered a certain way, not just that tiering exists as a policy
- Ongoing monitoring evidence: Transaction monitoring outputs, disposition records, and escalation logs — not a monitoring policy alone
- Change history: How and when controls were updated in response to new risk, not a static version-dated document
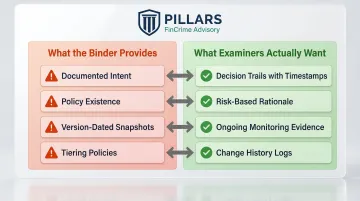
The binder approach fails because it was designed for a different regulatory era — one where documented intent was enough. Today's FinCrime examiners, particularly those reviewing fintechs and payments companies, expect real-time or near-real-time evidence of program operation.
A policy that hasn't been stress-tested against actual transaction data, alert volumes, or customer risk profiles isn't a compliance program. It's a starting point that was never finished.