Introduction
Regulatory exams at fintechs and financial institutions rarely fail due to bad intent. They fail because critical evidence is scattered across shared drives, workflows exist only in institutional memory, and compliance infrastructure wasn't architected to withstand the pressure of an examiner's scrutiny. When the FDIC ordered Piermont Bank in February 2024 to review all transactions since September 2022 for unreported suspicious activity, the issue wasn't a lack of controls—it was the inability to demonstrate those controls functioned consistently.
Audit readiness software closes that gap—transforming compliance from well-meaning procedures into an evidence-backed, exam-defensible program. This article covers the essential features compliance teams at fintechs, payments companies, and financial institutions should prioritize when evaluating audit readiness platforms, specifically for BSA/AML, KYC/CDD, and transaction monitoring.
TLDR
- Audit readiness software must link policies to controls to evidence—not just store documents
- Transaction monitoring documentation (alert rationale, tuning logs, SAR decisions) is critical and often missing from generic platforms
- Workflow automation should enforce compliance operating rhythm with task assignment, SLA tracking, and escalation
- Real-time dashboards and exam simulation reporting prove compliance rather than just suggest it
- Choose platforms that integrate with TM systems, case management, and KYC tools and scale with your risk footprint
Why Fintechs and Financial Institutions Need Purpose-Built Audit Readiness Software
Compliance vs. Audit Readiness
Compliance means controls exist; audit readiness means those controls are documented, tested, and producible on demand. The 2024 enforcement wave proves the distinction matters. Federal regulators issued consent orders against Piermont, Sutton, Thread, and Blue Ridge banks for failing to oversee fintech partners' BSA/AML programs—not because controls were absent, but because evidence of consistent execution was missing.
What Examiners Actually Request
BSA examiners from the OCC, FDIC, FinCEN, and state regulators don't just review policies during exams. They request:
- Evidence of consistent alert disposition with documented rationale
- SAR decision records (filed and declined)
- Training completion logs with dates and employee attribution
- Transaction monitoring tuning rationale and back-testing results
- Risk assessment documentation and approval trails
Generic document management systems aren't built around these deliverables. They store files but don't create the linkage examiners expect between policy intent and operational execution.
The Scaling Gap
Fintechs often scale faster than their compliance infrastructure. The Federal Reserve reported that mobile wallet payments grew from 2.9 billion transactions in 2018 to 14.4 billion in 2022—a nearly 5x increase. When transaction volumes surge, documentation gaps widen before teams even recognize the exposure. That's the problem purpose-built audit readiness software is designed to solve.

Centralized Evidence Management and Documentation Controls
The Foundation: Linked Evidence, Not Just Storage
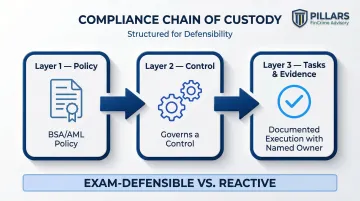
Audit readiness begins with a centralized evidence repository where every compliance artifact—policies, procedures, CDD records, SAR filings, training logs, risk assessments—lives in one auditable location. The differentiator isn't storage capacity; it's linkage. Strong platforms don't just house a BSA policy PDF—they connect that policy to:
- The control it governs
- The tasks that implement it
- Evidence proving it was followed, with a named owner at each step
This chain of custody makes audit responses defensible rather than reactive.
Version Control and Audit Trails
Every policy change, document approval, and access event must be timestamped and attributed to a named user. This matters during BSA exams because examiners don't just ask what the policy says today—they ask when it was last reviewed, who approved it, and what changed. 31 CFR 1020.320(d) mandates five-year retention for SARs and supporting documentation; a complete version history is what separates a credible response from a gap finding.
FinCEN's $80 million penalty against Canaccord Genuity in 2026 cited backdating and falsification of nearly 400 documents as an aggravating factor. Robust version control removes the temptation—and the opportunity—for exactly that kind of evidentiary failure.
Role-Based Access Controls
Only authorized personnel should edit or approve compliance documents, and the software must log who accessed what. This protects evidence integrity and supports segregation of duties—a cornerstone of BSA program governance.
Policy-to-Control Linkage
Most buyers focus on storage and overlook this capability. When an examiner asks, "How do you ensure your transaction monitoring policy is followed?" the answer can't be a binder pulled from a shelf—it has to be a traceable workflow showing the policy triggered a control, the control drove recurring tasks, and those tasks produced documented evidence. That's the difference between a program that looks good on paper and one that holds up under scrutiny.
Retention Policy Automation
Linkage only matters if records survive long enough to be examined. BSA regulations require five-year retention for SARs, CTRs, and CDD documentation, and manual tracking of those schedules is a known failure point. Audit readiness software should automate retention timelines and surface alerts before records risk improper deletion or quiet expiration.
Transaction Monitoring Documentation and Alert Disposition Tracking
How BSA Examiners Evaluate Alert Disposition
Generic compliance platforms don't have a concept of "alert disposition." But for BSA examiners, one of the most scrutinized areas is how compliance teams handle transaction monitoring alerts: what logic cleared or escalated the alert, who made the decision, and whether documentation was consistent.
Alert Disposition Tracking as a Software Feature
What it must include:
- Structured log where each alert disposition is recorded with:
- Analyst's rationale
- Supporting transaction data
- Date and timestamp
- Outcome (cleared, escalated to investigation, filed as SAR)
This log is the primary evidence that a TM program is functioning as designed. With industry false positive rates ranging from 90–95% and alert-to-SAR conversion rates between 0–5%, examiners expect firms to demonstrate quality control over dispositions — not just volume.

TM Model Tuning Documentation
Examiners expect firms to demonstrate that transaction monitoring thresholds and rules are periodically reviewed and justified. Under FRB SR 11-7 and OCC 2011-12, TM systems are treated as models requiring rigorous validation, data lineage tracking, and change control.
Audit readiness software should store and surface:
- Tuning rationale with retrieval on demand
- Back-testing results and validation documentation
- Model change logs linked to relevant policies or risk assessments
That model governance trail connects directly to SAR decision-making — when thresholds shift, examiners want to see that downstream filing decisions reflect those changes.
SAR Decision Documentation
Whether a SAR was filed or declined, the rationale needs documentation and retention. FinCEN clarified in October 2025 that documenting non-filing decisions isn't legally required, but FFIEC examiner procedures explicitly test whether non-filing rationale is supported and reasonable.
At minimum, the software needs to capture:
- Structured SAR workflow records
- Escalation history
- Supervisory review documentation
- Final filing or declination decision with rationale
Alert Quality Metrics and Reporting
Examiners use metrics to assess program effectiveness:
- False positive rates
- Alert-to-SAR conversion rates
- Workload distribution across analysts
- Average time to disposition
The software should generate these metrics directly from disposition data — no manual spreadsheet pulls. A compliance team that can produce a 12-month trend on false positive rates in minutes presents very differently to an examiner than one that scrambles to reconstruct it.
Policy Management, Workflow Automation, and Exam-Ready Reporting
Policy Management Beyond PDF Storage
Audit readiness platforms should support:
- Structured policy review cycles
- Automated reminders when policies are due for review
- Workflow for internal approval and attestation
Compliance officers must demonstrate to examiners that policies are living documents, not static files. FFIEC guidance emphasizes that documenting BSA/AML risk assessments in writing is a sound practice, and examiners must have access to independent testing scopes and supporting workpapers.
Meaningful Workflow Automation
Recurring compliance tasks should be automatable:
- Annual BSA risk assessment updates
- Periodic CDD reviews for high-risk customers (event-driven per FinCEN CDD Rule)
- Training completion tracking
- Independent testing schedules
Meaningful automation includes:
- Task assignment to specific owners
- SLA tracking with visibility into overdue items
- Escalation workflows when deadlines are missed
This differs from simple calendar reminders — it enforces the compliance operating rhythm and creates an auditable trail of who acted, when, and on what.
Exam Simulation and On-Demand Reporting
The best platforms let compliance teams generate a "regulatory exam package" on demand — structured to mirror exactly what an examiner would request. This eliminates the scramble when an exam notice arrives.
A complete exam package typically pulls together:
- Current and prior versions of relevant policies
- Evidence records tied to specific controls
- Training completion logs and attestations
- Independent testing results and remediation documentation
Staff Training and Attestation Tracking
31 CFR 1020.210 requires banks to provide training for appropriate personnel. Software should track:
- Training completion by employee
- Date of completion
- Content/curriculum covered
- Attestation records
FFIEC guidance states banks should document training programs, maintain attendance records, and document any failures to complete training timely, along with corrective actions. When examiners find incomplete records, they don't give the benefit of the doubt — they write a finding.
Integration Capabilities, Scalability, and How to Evaluate the Right Tool
Integration: Data Sync, Not Manual Uploads
Audit readiness software doesn't operate in isolation. It must pull data from:
- Transaction monitoring systems
- Case management platforms
- KYC/onboarding tools
- HR systems (for training records)
Real integration means automated data sync keeping your compliance records current at all times — not quarterly CSV uploads that create documentation lag.
Scalability for Growing Fintechs and Payments Companies
As transaction volumes grow, customer bases expand, and new product lines are added, the compliance program's documentation footprint grows with it. Software must be configurable to:
- Add new risk categories
- Accommodate new business lines
- Adapt to new regulatory requirements
- Scale without requiring re-implementation
This is especially critical for fintechs. P2P and money transfer payments grew from 1.6 billion in 2018 to 9.5 billion in 2022—a 6x increase. Compliance infrastructure must keep pace. Compliance infrastructure must keep pace, which makes choosing the right tool — and configuring it correctly — a decision worth evaluating carefully.

Evaluation Guidance for Compliance Teams
When selecting or upgrading tools:
- Prioritize platforms built for or deeply configurable for FinCrime use cases
- Ask vendors how their platform supports BSA exam preparation specifically
- Request demonstrations of alert disposition tracking, SAR workflow documentation, and TM tuning logs
- Evaluate integration capabilities with your existing tech stack
- Test whether the platform can generate exam-ready evidence packages on demand
Critical insight: The right software still requires expert configuration to reflect your program's actual risk profile. Pillars FinCrime Advisory works with compliance teams to assess whether current tools and documentation practices will hold up under regulatory scrutiny — and what needs to change before they do.
Frequently Asked Questions
Frequently Asked Questions
What are the features of an audit program?
A strong audit program includes a documented scope, risk-based testing methodology, evidence collection procedures, a findings and remediation workflow, and reporting to senior management or the board. In FinCrime contexts, this also covers transaction monitoring reviews, SAR quality assessments, and BSA risk assessment validation per FFIEC standards.
What are the 4 pillars of ITGC?
IT General Controls (ITGC) cover access controls, change management, computer operations, and system acquisition/development, as defined by ISACA's COBIT framework and PCAOB AS 2201. FinCrime compliance teams should confirm their audit readiness software meets access control and change management standards to protect evidence integrity.
What is the difference between audit readiness and being compliant?
Compliance means controls are in place; audit readiness means those controls are documented, consistently executed, and producible as evidence on demand. Software bridges that gap by making the proof of compliance as organized as the compliance program itself.
How does audit readiness software support BSA/AML regulatory exams specifically?
BSA examiners request consistent alert disposition records, SAR decision rationale, TM model tuning documentation, CDD records, and training logs. Audit readiness software centralizes and links these so they can be produced quickly and defensibly, reducing operational burden during exams.
Can smaller fintechs benefit from audit readiness software, or is it only for large institutions?
Smaller fintechs often face the same regulatory scrutiny as larger institutions but with fewer internal resources, making software that enforces documentation discipline especially valuable. The key is choosing a platform that scales with growth rather than requiring re-implementation as the program matures.
What should a compliance team do if their current software doesn't support FinCrime audit readiness?
Conduct a gap assessment comparing current documentation practices against what BSA examiners typically request, identify which features are missing, and either configure existing tools or evaluate purpose-built alternatives. Advisory support from firms like Pillars FinCrime Advisory ensures the resulting program is exam-defensible, not just better organized.