Introduction
Payment processors are getting hit from two directions at once. Fraud tactics—AI-powered attacks, synthetic identity schemes, account takeovers—are growing more sophisticated while businesses are simultaneously adding payment rails, onboarding new merchant segments, and facing tighter regulatory scrutiny. A fraud program built for last year's threat environment won't hold up under today's pressure.
The most effective fraud prevention programs aren't necessarily the most technologically advanced—they're the most adaptable. Flexibility in this context means building a program with modular controls, clearly documented risk appetite, and governance structures that can evolve without requiring a complete rebuild every time fraud patterns shift or the business adds a new product line.
This guide covers the foundational pillars of a scalable fraud program: designing detection logic that adapts to new threats, reducing false positives without compromising detection, and maintaining audit readiness as your operations grow.
TLDR
- Flexible fraud programs require documented risk appetite, layered controls, and governance—not just better technology
- Segment detection logic by fraud type (ATO, synthetic ID, first-party fraud) instead of relying on catch-all models
- Build "good customer" indicators alongside fraud signals to reduce false positives
- Bake audit readiness into program design from day one with proper policies and documentation
- Strategic partnerships help processors scale compliance capabilities faster than building internally
Why Payment Processors Need Flexible Fraud Prevention Programs
Payment processors occupy a uniquely vulnerable position in the financial ecosystem. As intermediaries connecting merchants, issuers, and consumers, they sit at the intersection of multiple fraud vectors—card-not-present fraud, first-party fraud, account takeover, and increasingly, AI-generated synthetic identities that exploit onboarding blind spots. According to LexisNexis Risk Solutions, ecommerce fraud attack rates surged 64% year-over-year, with gaming and gambling sites experiencing a 76% increase in attacks during 2025.
Static, rules-only fraud programs fail to keep pace because fraud patterns shift rapidly. Criminals often target specific merchant categories for brief windows (sometimes days or weeks) before moving to new targets.
A program that can't quickly adjust detection windows, recalibrate risk thresholds, or modify escalation paths will accumulate fraud losses and false positives simultaneously — driving up operational costs and customer friction at the same time.
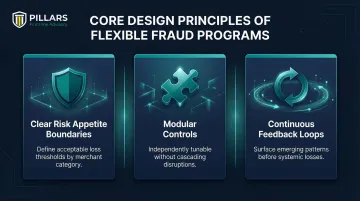
That operational pressure points to a clear design principle. Flexible fraud programs succeed not by offering more features, but by building in:
- Clear risk appetite boundaries that define acceptable loss thresholds across merchant categories
- Modular controls that can be tuned independently without cascading compliance disruptions
- Continuous feedback loops that surface emerging patterns before they become systemic losses
The Core Pillars of a Scalable Fraud Prevention Program
Pillar 1 — Risk Appetite and Policy Foundation
Every effective fraud program component traces back to a documented risk appetite statement. For payment processors, this means defining acceptable fraud loss thresholds by:
- Product type (ACH, card-not-present, real-time payments)
- Merchant category (high-risk verticals like gaming vs. low-risk retail)
- Transaction channel (mobile, web, API)
Fraud decisioning rules must be calibrated against these documented thresholds, not set arbitrarily. Without this foundation, rule-setting becomes arbitrary — and arbitrary programs don't hold up under regulatory examination.
Pillar 2 — Tiered Merchant and Customer Risk Segmentation
Risk-based segmentation allows processors to apply scrutiny proportional to actual risk. This includes segmenting by:
- Merchant risk profiles (business maturity, ownership transparency, compliance history)
- Transaction volumes and velocity patterns
- Business types and verticals
According to FDIC and OCC guidance, telemarketing and certain online merchants display disproportionately high unauthorized return and chargeback rates, requiring enhanced due diligence. Visa explicitly classifies specific MCCs as "High-Integrity Risk," including adult content, betting/gambling, outbound telemarketing, and cryptocurrency.
Without proper segmentation, programs either over-decline legitimate low-risk transactions or under-scrutinize high-risk activity—both costly outcomes.
Pillar 3 — Layered Detection Controls
Effective fraud detection stacks multiple independent control layers rather than relying on any single signal:
- Rules-based engines for known fraud patterns
- Behavioral analytics tracking user navigation and interaction patterns
- Device fingerprinting and reputation data
- Velocity checks across multiple dimensions
- Machine learning models for anomaly detection
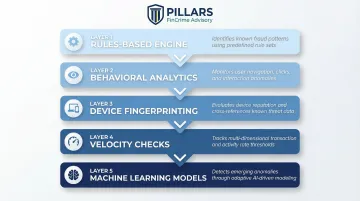
Each layer should be independently tunable and thoroughly documented. Changes to one layer shouldn't create blind spots in another—this requires governance and testing protocols that verify control effectiveness after modifications.
Pillar 4 — Feedback and Continuous Improvement Loop
A program that doesn't learn from its outcomes will drift. Confirmed fraud cases and false positive results need to feed directly into rule and model refinement through structured feedback mechanisms. Key components include:
- Case outcome tracking (fraud confirmed, false positive, inconclusive)
- Rule performance metrics (detection rate, false positive rate, coverage)
- Regular hypothesis testing for new detection signals
- Defined timelines for implementing rule changes based on findings
How quickly your team can test and deploy new detection hypotheses determines how fast the program improves. Slow iteration cycles let fraud patterns outpace your controls.
Pillar 5 — Governance and Escalation Structure
Governance makes fraud programs auditable and defensible. Essential elements include:
- Defined ownership of fraud controls (who owns which detection layers)
- Escalation protocols for high-risk cases
- Clear documentation of rule changes (what changed, why, who approved)
- Regular program reviews against documented risk appetite
- Training records demonstrating staff competency
Examiners don't just evaluate whether controls work — they look for evidence that decisions were intentional and risk-based. Strong operations without documented governance rarely survive a regulatory exam intact.
Designing Adaptive Detection Logic for Evolving Fraud Threats
Why Segmented Models Outperform Catch-All Approaches
A single fraud model trying to detect every threat type creates noise and blind spots. Different fraud types have distinct behavioral signatures:
- Account takeover (ATO): login anomalies, device changes, and navigation behavior shifts
- Synthetic identity fraud: fabricated but plausible identities built over time before monetizing
- First-party fraud: legitimate customers deliberately initiating chargebacks or payment reversals
Running purpose-built models against the same transaction data improves precision and reduces false positives compared to blunt, universal scoring. The sections below break down detection logic for each of these fraud types.
Account Takeover Detection
Effective ATO detection requires behavioral analytics that track:
- Typing patterns and interaction cadence
- Navigation behavior compared to historical baselines
- Device fingerprinting and geolocation consistency
- Login anomalies (time of day, frequency, failed attempts)
These signals differ fundamentally from transaction-level fraud indicators. Identity verification steps should layer into existing flows without adding friction at every touchpoint — step-up authentication triggered by anomaly scores, not applied universally.
Synthetic Identity and Application Fraud
Synthetic ID fraud exploits onboarding blind spots—fraudsters build plausible-looking identities over time before monetizing them through high-value transactions or credit abuse. Effective detection requires:
- Cross-referencing identity data points (SSN age and issuance patterns, phone number history, address consistency)
- Incorporating reputational data from third-party sources or industry consortia
- Monitoring velocity of new account applications sharing identity attributes
- Tracking identity element reuse across multiple applications
Real-Time Payment Fraud Controls
Real-time payment rails present unique challenges—once funds move, recovery is difficult or impossible. This makes pre-authorization controls especially critical:
- Confirmation of payee (validating recipient identity before release)
- Velocity limits calibrated to customer and merchant risk tiers
- Risk-scored pre-screening that evaluates transactions before authorization
- Enhanced monitoring for new payment relationships
Adaptive Risk Signal Windows
Static time windows for measuring fraud behavior (for example, analyzing merchant risk over a fixed 12-month period) miss short-burst fraud patterns where criminals exploit a target for days or weeks before moving on.
Detection logic should use dynamic windows calibrated to observed fraud exploitation cycles:
- Short windows (24-72 hours) for rapid-onset fraud patterns
- Medium windows (7-30 days) for evolving merchant risk
- Long windows (90+ days) for baseline behavioral profiling
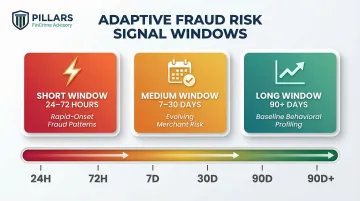
Window selection should be documented and tied to specific fraud typologies, not default reporting periods.
Reducing False Positives Without Compromising Detection
Most false positive problems aren't tuning problems—they're design problems. High false positive rates typically signal that detection logic isn't properly segmented or calibrated for the customer population it's scoring. The consequences compound quickly:
Why False Positives Are a Design Problem
- Operational friction as investigation teams chase low-quality alerts
- Customer experience damage from unnecessary declines
- Abandoned transactions and revenue loss
- Alert fatigue reducing investigator effectiveness
Addressing this means examining how rules are structured, how customer populations are segmented, and whether positive behavioral signals are factored into decisioning at all.
Good Customer Scoring as a Counterbalance
Building positive behavioral indicators alongside fraud risk scores prevents penalizing legitimate customers who happen to trigger fraud-focused rules. Good customer signals include:
- Consistent bill pay history
- Stable account activity patterns over time
- Direct deposit relationships
- Long-standing merchant relationships
- Verified identity elements across multiple sources
When a transaction triggers fraud rules but the customer has strong positive indicators, the system can route to lower-friction review processes rather than automatic decline.
Operational Benefits of Better Alert Quality
Fewer false positives means investigation teams focus on genuine risk signals. This creates a compounding operational benefit:
- Faster case decisions with higher accuracy
- Reduced investigator burnout and turnover
- Clearer fraud patterns to train from, improving investigator skill over time
- Stronger regulatory exam performance, with documented evidence of effective risk management
Keeping Your Program Audit-Ready as You Scale
What Examiners Look For
Regulators and examiners evaluate payment processor fraud programs based on:
- Documented risk appetite — clear statements of acceptable risk levels
- Calibrated controls — evidence that detection rules align with actual risk exposure
- Governance trail — documentation showing who approved rule changes and why
- Program testing and validation — evidence of ongoing effectiveness reviews
Many operationally effective programs still fail exams because documentation doesn't demonstrate a deliberate, risk-based approach. Performance alone isn't enough—you must show intentionality.
Periodic Fraud Risk Assessments
Formal fraud risk assessments—conducted at least annually and triggered by significant changes—keep controls aligned with actual exposure. Payment processor assessments should cover:
- Transaction volume growth and velocity changes
- New merchant segments or high-risk verticals added
- New payment rails or product launches
- Emerging fraud typologies affecting the industry
- Changes in chargeback or dispute patterns
These assessments provide the documented justification for control adjustments, demonstrating proactive risk management rather than ad hoc adjustments.
Policy Documentation Framework
The fraud program's policy framework should include:
- Fraud risk policy — risk appetite, governance structure, control principles
- Detection and response procedures — how fraud is identified and escalated
- Escalation protocols — decision authority and review requirements
- Model/rule change logs — audit trail of detection logic modifications
- Training records — documentation of staff competency and knowledge
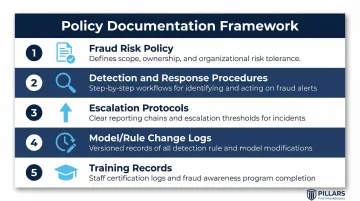
This documentation isn't bureaucratic overhead—it's what allows examiners to verify your program is intentional and risk-based.
When Governance Lags Behind Growth
Growing payment processors often find their program governance can't keep pace with transaction volume expansion. Controls adequate at launch become insufficient as merchant portfolios grow or new payment products are added.
For processors navigating this gap, working with a specialized partner can close it faster than building internal capacity from scratch. Pillars FinCrime Advisory supports payment companies through the full program lifecycle—policy development, transaction monitoring optimization, and regulatory exam readiness—helping teams get to a defensible compliance posture without adding headcount.
Frequently Asked Questions
What are effective methods of combating payment fraud?
Effective fraud prevention uses a layered approach: segmented detection models by fraud type, behavioral analytics tracking user patterns, reputational data integration from third-party sources, identity verification at onboarding, and continuous feedback loops refining detection rules—all calibrated against a documented risk appetite.
What is the 10/80-10 rule for fraud?
The 10/80-10 rule suggests 10% of fraud decisions are clearly fraudulent, 80% require nuanced judgment across multiple signals, and 10% are clearly legitimate. Program design should focus on getting that ambiguous middle right through intelligent detection and well-calibrated risk thresholds.
What makes a fraud prevention program "flexible"?
Flexibility means the program is built with modular, documented controls that can be adjusted as threats evolve—including tunable detection windows, segmented fraud models addressing specific threat types, a clear risk appetite policy guiding rule changes, and a governance structure that doesn't require complete rebuilds every time fraud patterns shift.
How often should payment processors review and update their fraud prevention programs?
Conduct formal fraud risk assessments at least annually, with triggered reviews whenever significant changes occur—new payment rails launched, merchant portfolio expansion into new verticals, emerging fraud typologies affecting the industry, or notable changes in chargeback volumes or loss rates that signal shifting risk exposure.
What is the difference between fraud prevention and AML compliance for payment processors?
Fraud prevention protects processors, merchants, and consumers from financial loss through deceptive activity like unauthorized transactions and identity theft. AML compliance focuses on detecting and reporting transactions tied to criminal proceeds or terrorist financing. The programs are distinct but increasingly interconnected—fraudsters often exploit payment processors for both.