
Introduction
A payments processor onboarding thousands of customers daily or a crypto exchange handling cross-border transfers around the clock cannot rely on quarterly spreadsheet reviews. As transaction volume scales, so does financial crime exposure—and traditional manual risk assessment methods cannot keep pace with the velocity, complexity, or sophistication of modern money laundering and fraud schemes.
Regulators have noticed. FinCEN, FFIEC, and FATF now expect dynamic, documented risk assessments—not annual snapshots frozen in time. FinCEN's proposed AML program reforms explicitly state that institutions must "not simply maintain static risk assessments" but rather use a "dynamic and recurrent risk assessment process" updated when material changes occur.
Firms still running manual processes face real consequences: exam findings, enforcement actions, and compliance teams dedicating up to 10–15% of full-time staff to KYC/AML operations alone—often drowning in false positives that exceed 98%.
This guide explains how automated risk assessment replaces static scoring with continuous, data-driven models—and how banks, fintechs, and crypto firms can build scalable, regulator-aligned compliance programs.
TLDR
- Automated risk assessment replaces static scoring with continuous models that update as customer behavior and risk signals change
- Covers entity risk, transaction behavior, geographic exposure, product/channel risk, and crypto-specific blockchain analytics
- Reduces false positives, accelerates onboarding, and produces audit-ready documentation regulators expect
- Addresses BSA/AML, FinCEN CDD Rule, and FATF Travel Rule requirements at scale
What is Automated Risk Assessment in Financial Crime Compliance?
Automated risk assessment uses technology—rules-based engines, machine learning models, and integrated data feeds—to score, tier, and monitor the financial crime risk posed by customers, transactions, and business relationships. It replaces manual analyst-driven processes with scalable systems capable of evaluating thousands of risk signals simultaneously.
Critical distinction: This is not IT security or cyber risk assessment. FinCrime risk assessment specifically addresses AML/BSA exposure, KYC completeness, sanctions risk, and the likelihood that a customer or transaction connects to money laundering, fraud, or financial crime.
How automation differs from manual approaches:
Manual programs run on calendar schedules—annual or quarterly reviews—that freeze a customer's risk profile at a single point in time. Automated systems work differently. Risk scores update continuously in response to live inputs: new transactions, adverse media hits, sanctions list changes, and behavioral anomalies. The result is a dynamic risk profile that reflects current reality, not last quarter's snapshot.
Instead of waiting for the next scheduled review, automated systems detect when a customer's business type changes, when adverse media surfaces, or when transaction patterns deviate from baseline. Risk score updates happen as those signals emerge, not months later.
Why Manual Risk Assessment No Longer Works
The Volume and Velocity Problem
Fintechs onboard thousands of new customers per day. Crypto platforms process transactions 24/7 across global jurisdictions. Banks manage millions of accounts. Manual risk scoring at this scale is operationally impossible without cutting corners, creating inconsistent tiering and undetected risk gaps.
McKinsey research confirms that banks commonly assign 10-15% of full-time equivalents to KYC/AML operations alone, while legacy customer-risk rating and transaction monitoring models exhibit false positive rates exceeding 98%. This operational burden diverts critical resources away from actual high-risk investigations, creating capacity constraints that leave teams perpetually reactive.
The Regulatory Blind Spot
Manual systems operate on fixed review cycles—annual, semi-annual, or quarterly. Financial crime patterns can emerge and escalate between these scheduled reviews, with no mechanism to detect mid-cycle changes in customer behavior, new adverse news, or emerging typologies.
FinCEN's proposed AML program rules make the regulatory expectation explicit: institutions must maintain a "dynamic and recurrent risk assessment process" updated periodically and when material changes occur. A frozen spreadsheet updated once annually no longer satisfies this standard.
The False Positive Crisis
According to a 2024 LexisNexis report, firms now automate an average of 80% of CDD processes—and the compliance leaders driving that shift report measurable results. Among those expecting continued automation gains:
- 63% anticipate improved data quality
- 46% expect better identification of high-risk customers
- 35% project faster onboarding cycle times

These figures point to one conclusion: automation addresses the operational pain points that manual processes cannot.
Key Risk Dimensions: What Gets Assessed Across Banks, Fintechs & Crypto
Customer and Entity Risk
Customer risk scoring evaluates multiple dimensions simultaneously:
- Customer type (individual, business, MSB, PEP)
- Industry or occupation
- Beneficial ownership complexity
- Adverse media presence
- Jurisdiction of residence or incorporation
These systems pull from sanctions and PEP databases, corporate registries, and adverse media monitoring services to score each dimension and produce a composite customer risk rating. That rating determines onboarding requirements and ongoing monitoring intensity.
Risk tiering links directly to due diligence requirements. Standard versus enhanced due diligence (EDD) triggers are built into scoring logic, reducing subjective analyst decisions and ensuring consistent application of the institution's risk methodology.
Transaction and Behavioral Risk
Transaction risk assessment evaluates:
- Transaction volume and velocity
- Counterparty identity and risk profile
- High-risk corridor activity (jurisdictions, currencies)
- Patterns inconsistent with customer's stated profile
Behavioral analytics detect deviations from a customer's established baseline—an early indicator of account compromise, structuring, or layering activity. When a business customer whose typical monthly transaction volume is $50,000 suddenly processes $500,000 in peer-to-peer transfers, the platform flags the anomaly for review.
Geographic and Jurisdictional Risk
Transaction-level risk feeds directly into geographic exposure. Geographic risk scoring integrates:
- FATF grey and blacklists
- OFAC sanctioned jurisdictions
- High-risk country designations
- Correspondent banking exposure
As of February 2026, the FATF "black list" includes North Korea, Iran, and Myanmar. Dynamic geographic risk weights update automatically when regulatory bodies revise country assessments, eliminating the lag inherent in manually maintained country risk matrices.
Product, Channel, and Delivery Risk
Geographic risk is only one layer. Products and delivery channels introduce their own inherent risk levels:
- Peer-to-peer transfers
- Embedded finance APIs
- Instant payment rails
- Anonymous prepaid products
Risk scoring incorporates product and channel risk as separate dimensions. A mobile wallet offering instant international transfers carries a different risk profile than a traditional checking account, and the scoring engine applies those differences consistently across the customer base.
Crypto and Virtual Asset Risk
Crypto firms and institutions offering virtual asset services face risk dimensions that traditional frameworks do not address:
Blockchain transaction analytics:
- Wallet risk scoring
- Exposure to mixing services
- Darknet market connections
- Peer-to-peer exchange activity
Counterparty risk at the entity level adds a second layer of exposure. VASP counterparty risk covers:
- Counterparty VASP due diligence
- FATF Travel Rule compliance
- DeFi protocol interactions where counterparty identity is obscured
According to the Chainalysis 2024 Crypto Crime Report, illicit cryptocurrency addresses received at least $24.2 billion in 2023—representing 0.34% of total on-chain transaction volume. Sanctioned entities and jurisdictions accounted for $14.9 billion, or 61.5% of all illicit transaction volume measured.
Leading blockchain analytics platforms:
- Chainalysis KYT: Scores scams, darknet markets, and sanctioned entities with customizable severity thresholds
- Elliptic Lens: Configurable risk rules covering mixers, darknet markets, and sanctioned wallets
- TRM Labs Wallet Screening: Over 155 configurations covering ownership, counterparty, and indirect risk with confidence scores

General AML frameworks weren't built for on-chain activity. Crypto-focused risk models must integrate blockchain intelligence directly into scoring logic to identify illicit exposure at the wallet and transaction level.
How Automated Risk Assessment Works: A Step-by-Step Breakdown
Step 1: Define Risk Appetite and Scoring Methodology
Effective automated risk assessment starts with documented risk appetite statements defining the institution's tolerance for financial crime exposure across four key dimensions:
- Customer type — retail, commercial, institutional, or high-risk categories
- Product — payment rails, lending, custody, or crypto services
- Geography — domestic vs. cross-border, high-risk jurisdictions
- Channel — digital onboarding, branch, third-party referrals
Risk weighting factors must be calibrated to the specific business model. A neobank serving gig economy workers carries a different inherent risk profile than a crypto exchange serving institutional clients. The scoring methodology should reflect these differences with transparent, defensible logic.
Step 2: Integrate Data Sources
Automated risk systems require comprehensive data feeds:
Internal data:
- Customer and transaction data
- Account activity patterns
- Product and channel usage
External data:
- Sanctions and PEP screening databases
- Adverse media monitoring
- Beneficial ownership registries
- Credit and identity verification data
- Blockchain analytics platforms (for crypto firms)
The quality and breadth of data integration determines the accuracy of automated risk scoring. Incomplete data feeds create coverage gaps that compromise the entire system.
Step 3: Automated Risk Scoring and Customer Tiering
Rules-based engines or machine learning models apply defined weighting factors to produce a composite risk score. Customers are then segmented into tiers:
| Risk Tier | Onboarding Treatment | Monitoring Intensity |
|---|---|---|
| Low | Standard onboarding | Routine |
| Medium | Enhanced documentation | Moderate |
| High | Enhanced due diligence (EDD) | Intensive |
| Unacceptable | Account denied or exited | N/A |

Tiering logic dictates onboarding friction, due diligence depth, transaction monitoring parameters, and review frequency. All tiering decisions should be documented and defensible for regulatory examination.
Step 4: Continuous Monitoring and Risk Score Refresh
Automated systems monitor accounts and transactions on an ongoing basis, triggering risk score updates when defined conditions are met:
- Sanctions list match
- Adverse media alert
- Transaction pattern anomaly
- Change in business type
- Geographic risk reclassification
This keeps risk profiles current, replacing the stale snapshots that periodic manual review cycles inevitably produce.
Step 5: Escalation, SAR Trigger Logic, and Audit Trail
Automated systems route high-risk alerts to analyst queues for review and disposition. When thresholds are met, they generate Suspicious Activity Report (SAR) filing triggers and produce complete, timestamped audit trails.
A defensible audit trail documents:
- Every risk scoring event
- All data inputs and sources
- Analyst actions and dispositions
- Policy and threshold changes
- System configuration updates
This documentation is essential for regulatory examinations and enforcement inquiries.
Regulatory Requirements: BSA, AML, FinCEN, and Crypto-Specific Rules
Foundational Framework for Banks and Fintechs
The Bank Secrecy Act (BSA) requires covered institutions to establish AML programs with a risk-based customer identification and due diligence process. The FinCEN Customer Due Diligence (CDD) Final Rule formalized requirements for beneficial ownership identification and risk-based ongoing monitoring.
In February 2026, FinCEN issued Exceptive Relief (FIN-2026-R001) streamlining beneficial ownership requirements. Institutions are no longer required to identify and verify beneficial owners at each new account opening — only at initial onboarding and when ongoing monitoring raises questions about information reliability.
The FFIEC BSA/AML Examination Manual sets clear examiner expectations for risk assessments. According to the Manual, a sound risk assessment must:
- Analyze risks across products, services, customers, and geographic locations
- Be updated when new products or customer types are introduced
- Be refreshed when the institution expands into new markets or channels
Fintech and Crypto-Specific Regulatory Considerations
Money Services Businesses (MSBs): Fintechs operating as MSBs under FinCEN registration face BSA obligations. Those operating under a sponsor bank relationship must satisfy the bank's BSA/AML program requirements.
Virtual Asset Service Providers (VASPs): FinCEN's 2013 virtual currency guidance established that administrators and exchangers of convertible virtual currency are MSBs subject to AML and registration requirements. The FATF Travel Rule applies Recommendation 16 to VASPs, requiring transmission of originator and beneficiary information for virtual asset transfers above $1,000.
State licensing regimes: New York's BitLicense framework requires licensees to conduct initial AML risk assessments and additional assessments "on an annual basis, or more frequently as risks change," modifying AML programs accordingly.
Recent Enforcement Actions
FinCEN's $29 million enforcement action against Bittrex found the exchange's AML program failed to appropriately address risks associated with anonymity-enhanced cryptocurrencies and relied on an "ineffective manual transaction review process." The 2023 Binance consent order highlighted that the exchange operated for over a year with no AML program, and its subsequent program was ineffective—explicitly ordering the implementation of "Periodic Risk Assessments" as part of remediation.
Both cases share a common thread: regulators didn't just penalize weak controls — they mandated periodic, documented risk assessments as the baseline for remediation. Institutions that treat risk assessment as a one-time exercise rather than an ongoing process face the same exposure.
Best Practices for Building a Scalable Automated FinCrime Risk Program
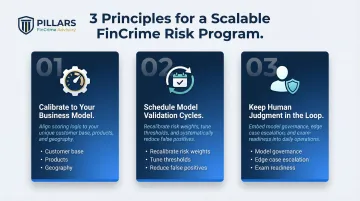
Three principles separate compliance programs that scale cleanly from those that create regulatory exposure as they grow:
Calibrate to your business model. A payments processor, a crypto exchange, and a community bank face fundamentally different risk profiles. Scoring logic, risk weighting, and due diligence thresholds need to reflect your specific customer base, products, and geographic footprint—then get revalidated as the business changes.
Schedule model validation cycles. Automated risk models drift. Customer populations shift, transaction patterns evolve, and regulatory expectations move. Regular validation reviews let you recalibrate risk weights and tune monitoring thresholds to cut false positives without opening gaps that miss genuine financial crime.
Keep human judgment in the loop. Automation handles volume and speed; it doesn't replace model governance, edge case escalation, or regulatory dialogue. CAMS-certified compliance expertise remains essential for interpreting complex risk scenarios, managing exam preparation, and keeping the program audit-ready.
For firms building or optimizing a FinCrime risk assessment program, Pillars FinCrime Advisory provides hands-on advisory support—from risk methodology design and policy development to transaction monitoring optimization and regulatory exam readiness.
Founder Joshua Douglas brings 12+ years in financial crime and nearly 20 years across financial services. His clients—fintechs, payments companies, and financial institutions—have used that experience to build compliance programs that hold up under regulatory scrutiny as they scale.
Frequently Asked Questions
What are the 5 C's of risk assessment?
The "5 C's of credit" is a traditional credit-underwriting framework used by lenders to evaluate borrower default risk—not an AML or financial crime standard. It does not apply to FinCrime compliance documentation.
What are the 4 types of risk assessment?
Compliance frameworks distinguish four types: qualitative (expert judgment and descriptive categories), quantitative (numerical scoring and statistics), semi-quantitative/hybrid (blending both), and continuous/dynamic assessments that update risk profiles based on behavioral triggers rather than static periodic reviews.
How does automated risk assessment differ for crypto firms compared to traditional banks?
Crypto firms must incorporate blockchain analytics and on-chain behavioral data, score VASP counterparty risk, and address FATF Travel Rule compliance—dimensions that traditional bank risk models don't account for. Specialized platforms score wallet exposure to mixing services, darknet markets, and sanctioned entities.
What triggers a risk assessment update or refresh?
Common triggers include a sanctions or adverse media alert, unusual transaction activity, a change in customer business type or beneficial ownership, a regulatory list update, or a defined periodic review schedule. Automated systems detect these triggers and update risk scores in real time.
What regulatory requirements mandate risk assessments for fintechs and crypto firms?
Key regulatory drivers include the Bank Secrecy Act (BSA), FinCEN CDD Final Rule, FinCEN virtual currency guidance, FATF Travel Rule, and state MSB/VASP licensing requirements such as New York's BitLicense. All require documented, risk-based compliance programs.
How does automated risk assessment improve transaction monitoring effectiveness?
Automated risk tiering informs transaction monitoring thresholds—high-risk customers receive tighter alert parameters, while low-risk accounts generate fewer false positives. The result is higher alert quality and better analyst efficiency across the board.


